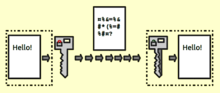
In cryptography, encryption is the process of encoding a message or information in such a way that only authorized parties can access it and those who are not authorized cannot. Encryption does not itself prevent interference, but denies the intelligible content to a would-be interceptor. In an encryption scheme, the intended information or message, referred to as plaintext, is encrypted using an encryption algorithm – a cipher – generating ciphertext that can be read only if decrypted. For technical reasons, an encryption scheme usually uses a pseudo-random encryption key generated by an algorithm. It is in principle possible to decrypt the message without possessing the key, but, for a well-designed encryption scheme, considerable computational resources and skills are required. An authorized recipient can easily decrypt the message with the key provided by the originator to recipients but not to unauthorized users.
Types
Symmetric key / Private key
In
symmetric-key schemes,
[1] the encryption and decryption keys are the same. Communicating parties must have the same key in order to achieve secure communication.
Public key
In
public-key encryption schemes, the encryption key is published for anyone to use and encrypt messages. However, only the receiving party has access to the decryption key that enables messages to be read.
[2] Public-key encryption was first described in a secret document in 1973;
[3] before then all encryption schemes were symmetric-key (also called private-key).
[4]:478. Although published subsequently, the work of Diffie and Hellman, was published in a journal with a large readership, and the value of the methodology was explicitly described
[5]and the method became known as the Diffie Hellman key exchange.
A publicly available public key encryption application called
Pretty Good Privacy (PGP) was written in 1991 by
Phil Zimmermann, and distributed free of charge with source code; it was purchased by
Symantec in 2010 and is regularly updated.
[6]
Uses
Encryption has long been used by militaries and governments to facilitate secret communication. It is now commonly used in protecting information within many kinds of civilian systems. For example, the
Computer Security Institute reported that in 2007, 71% of companies surveyed utilized encryption for some of their data in transit, and 53% utilized encryption for some of their data in storage.
[7] Encryption can be used to protect data "at rest", such as information stored on computers and storage devices (e.g.
USB flash drives). In recent years, there have been numerous reports of confidential data, such as customers' personal records, being exposed through loss or theft of laptops or backup drives; encrypting such files at rest helps protect them if physical security measures fail.
[8][9][10] Digital rights management systems, which prevent unauthorized use or reproduction of copyrighted material and protect software against
reverse engineering (see also
copy protection), is another somewhat different example of using encryption on data at rest.
[11]
In response to encryption of data at rest, cyber-adversaries have developed new types of attacks. These more recent threats to encryption of data at rest include cryptographic attacks,
[12] stolen ciphertext attacks,
[13] attacks on encryption keys,
[14] insider attacks, data corruption or integrity attacks,
[15] data destruction attacks, and
ransomware attacks. Data fragmentation
[16] and
active defense[17] data protection technologies attempt to counter some of these attacks, by distributing, moving, or mutating ciphertext so it is more difficult to identify, steal, corrupt, or destroy.
[18]
Message verification
Digital signature and encryption must be applied to the ciphertext when it is created (typically on the same device used to compose the message) to avoid tampering; otherwise any node between the sender and the encryption agent could potentially tamper with it. Encrypting at the time of creation is only secure if the encryption device itself has not been tampered with.
Data erasure
Conventional methods for
deleting data permanently from a storage device involve overwriting its whole content with zeros, ones or other patterns – a process which can take a significant amount of time, depending on the capacity and the type of the medium. Cryptography offers a way of making the erasure almost instantaneous. This method is called
crypto-shredding. An example implementation of this method can be found on
iOS devices, where the cryptographic key is kept in a dedicated 'Effaceable Storage'.
[22] Because the key is stored on the same device, this setup on its own does not offer full confidentiality protection in case an unauthorised person gains physical access to the device.



Comments
Post a Comment